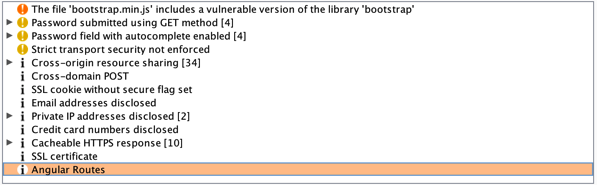
When it comes to testing for security within our web applications, we often look to creating simple tools to help speed things up. They also help provide a consistent way to help identify known patterns. For those that haven't been following, I have been doing a few posts about getting the OWASP Juice Shop application up and running. In this post, I want to introduce a simple burp extension I created to help with a few of the challenges presented in the OWASP Juice … [Read more...] about Burp Extension – Juice Shop Routes
application security
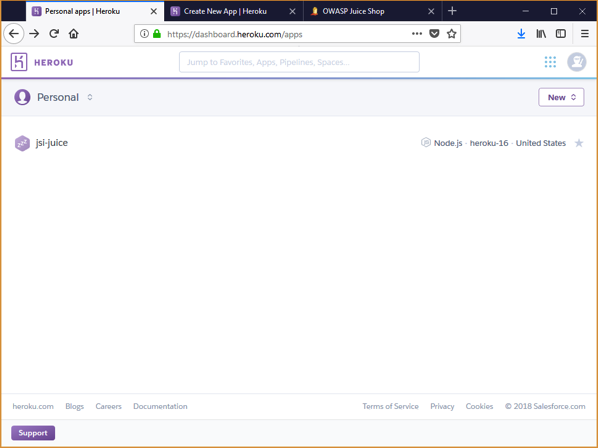
Installing OWASP JuiceShop with Heroku
I am often asked the question by clients and students where people can go to learn hacking techniques for application security. For years, we have had many purposely vulnerable applications available to us. These applications provide a safe environment for us to learn more about hacking applications and the vulnerabilities that are exposed without the legal ramifications. In this post I want to show you how simple it is to install the OWASP Juice Shop application using Heroku. Juice Shop is a … [Read more...] about Installing OWASP JuiceShop with Heroku
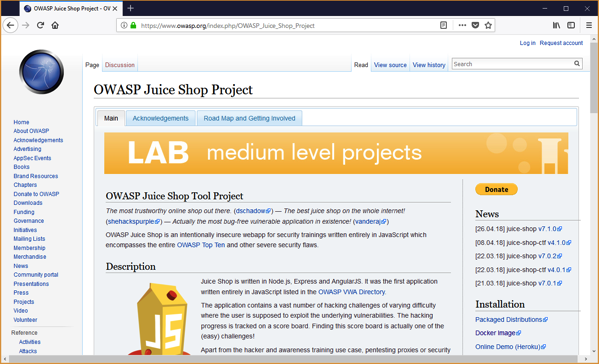
Installing OWASP JuiceShop with Docker
I am often asked the question by clients and students where people can go to learn hacking techniques for application security. For years, we have had many purposely vulnerable applications available to us. These applications provide a safe environment for us to learn more about hacking applications and the vulnerabilities that are exposed without the legal ramifications. In this post I want to show you how simple it is to install the OWASP Juice Shop application using a Docker container. … [Read more...] about Installing OWASP JuiceShop with Docker
OWASP 2017 Changes
When I talk to people about application security, the most recognized topics is the OWASP Top 10. If you haven't heard of the top 10, or need a refresher, you can get the full list at: https://www.owasp.org/images/7/72/OWASP_Top_10-2017_%28en%29.pdf.pdf The OWASP Top 10 is on a three year update cycle. We had the list in 2010, 2013 and now the latest is 2017. You may be wondering why it is 2017 rather than 2016. I think that is a question a lot of people had. In any case, the list made it out … [Read more...] about OWASP 2017 Changes
Two-Factor Authentication Considerations
There was a recent article talking about how a very small percentage of google users actually use 2-factor authentication. You can read the full article at http://www.theregister.co.uk/2018/01/17/no_one_uses_two_factor_authentication/ Why 2-Factor Two-factor authentication, or multi-factor authentication, is a valuable step in the process to protect accounts from unauthorized users. Traditionally, we have relied just on a username/password combination. That process had its own weaknesses that … [Read more...] about Two-Factor Authentication Considerations
Tinder Mobile Take-Aways
While browsing through the news I noticed an article talking about the Tinder mobile app and a privacy concern. You can read the article at https://www.consumerreports.org/privacy/tinder-app-security-flaws-put-users-privacy-at-risk/. To summarize what is considered the issue is that the mobile application does not transmit the photos that you see using HTTPS. This means that anyone on the same connection can see the traffic and, ultimately, see the photos you are presented. From my … [Read more...] about Tinder Mobile Take-Aways